10金币
|
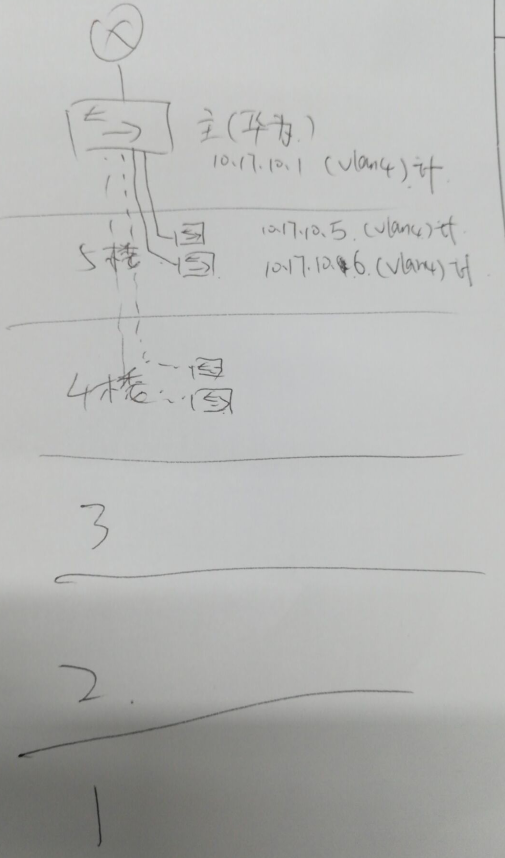
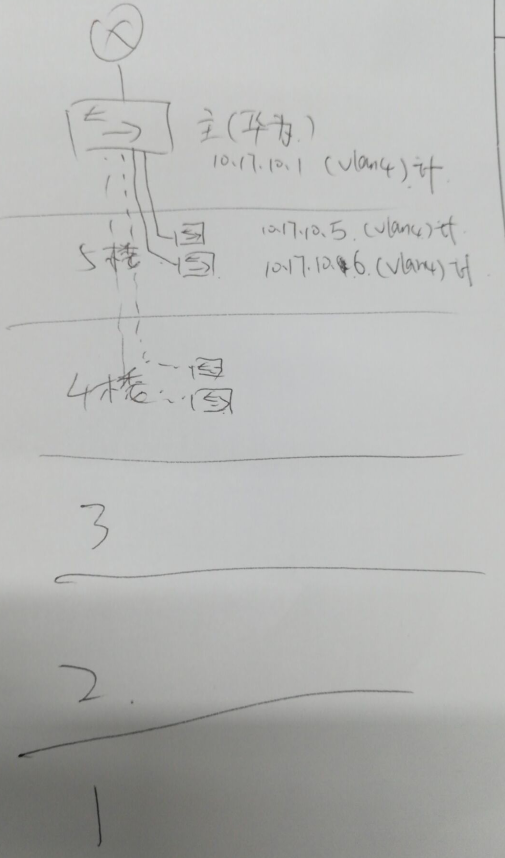
交换机配置的vlan if的ip地址ping不通,可以从哪里找原因呢
8 y$ d2 y4 q g. t* M+ b% N0 o0 j# @# \8 u) M: Y! u, Y
我这边交换机配置的vlan if的ip地址ping不通,可以从哪里找原因呢
6 A% M/ K1 `7 y' `5 J; Z$ a
, u' K- K a9 e2 \, a1 |4 e6 \% {$ ]<sw-5-2>display current-configuration 5 ?( [; T, w8 M1 {8 Q
!Software Version V200R007C00SPC500
! o/ B1 `6 s" f2 V3 k# f0 k7 e( p8 ?5 @0 c# i; Q. i% J
sysname sw-5-2
1 v* b- b$ @* W H- _#7 e" m& x$ r3 J7 D( G1 d
vlan batch 2 to 7
# k/ f) p% I- p& @. w- ?2 |0 J#) {9 \) Y6 j1 Q. k- T L
stp mode rstp
" b8 t0 v, ~3 Z( {+ y: r#
7 o: G9 M$ n4 A: T$ Utelnet server enable
7 z8 D$ j2 j9 q. [3 n3 l#
- C/ R2 B! u# k1 N/ G# P, Yclock timezone Indian Standard Time minus 05:13:20
. U. G3 C) I" k% {- W, Z#
% q. ]9 F$ I! `! O Adhcp enable
2 g; o( M+ U q7 s+ s4 p# B1 S) P#6 H6 k6 o, ^2 k( P% Y. l$ A
aaa
' C ~# E/ e# V: p6 R, Z2 I4 {! u authentication-scheme default) G0 ?- ?( E$ ^& k7 R- w& J K
authorization-scheme default1 d) o! O. k% r
accounting-scheme default
1 T; i/ \! E/ o$ ]5 n" | domain default2 `) _( ?7 C. }. z4 H7 J
domain default_admin# m0 t( O/ J* i( L; A
local-user admin password irreversible-cipher %#%#8(M{.}0139Z[(hCxEL'){,KL+i1l[FZ%2R({pqI5!etf<o8E)0Uu"qIAf/&R%#%#
7 y- |# M7 s, M local-user admin privilege level 15, l- w+ V4 T' X! q% S- \
local-user admin service-type telnet7 q4 N) }/ L6 Q4 z
#
8 L& Y8 D. q; L1 Tinterface Vlanif1
2 l; ]) k# n. J8 J$ C#
6 T# p# g$ r% g9 w: o1 C: `interface Vlanif4: N/ G3 r5 G0 |3 e% p0 _
ip address 10.17.10.6 255.255.255.128
$ g+ g5 Z& F7 W, ^0 m#5 @! ~+ Q( `+ `
interface GigabitEthernet0/0/1
! s+ N4 z; z+ X3 s) q ]- M5 E#
% c; D" K6 B+ j& A. A- r( Vinterface GigabitEthernet0/0/2
2 r; N8 R$ G7 u/ d" m#6 h w6 \: h$ P
interface GigabitEthernet0/0/3& ]. ?! R9 s$ z% |
#
8 {$ m) K/ U4 w) @+ pinterface GigabitEthernet0/0/4
8 j" p! r1 Y3 A#9 L5 j. O ^ z1 [( D8 n5 l8 k
interface GigabitEthernet0/0/5. F3 T% h: ?* V, q4 L* c
#$ y1 Z) |4 m$ o0 n2 `9 q4 A
interface GigabitEthernet0/0/67 ]$ y/ `. K- p
#2 @; ?0 d8 c* ~5 H
interface GigabitEthernet0/0/7
; i. R) M* V' A/ X& M#
& B8 Z/ d: a% P1 O2 E5 J' [7 ?interface GigabitEthernet0/0/8% e* @( N* E* M( C$ {+ n
#: ]( M0 ]; N" D1 ~- M; n
interface GigabitEthernet0/0/9
^3 K4 g7 v2 J# u* A3 k8 f9 p#
, c6 T$ T+ @+ ?& g. [! _interface GigabitEthernet0/0/10
: k, |5 p$ p- I; g# i# ! Z, E) i- Q; |9 i" ^# ?
interface GigabitEthernet0/0/113 y, D0 {2 Z0 R2 b$ M+ x S0 N
#) }6 g; m' C8 b, w
interface GigabitEthernet0/0/12
1 \# D8 R/ N' j# k. `) C) L; w
interface GigabitEthernet0/0/13% a" ]0 g# K8 q9 f) z
#
% T& }: ]/ c" `1 Ointerface GigabitEthernet0/0/14
- |$ a8 f u; F#$ f! X7 O V* W& T* I
interface GigabitEthernet0/0/15+ m8 O6 Y1 u }
#' f9 i7 [, }) w, N$ j: C
interface GigabitEthernet0/0/16
, j' n+ T$ V& h#- \. Q( B. L) q: E, _
interface GigabitEthernet0/0/176 M+ f) \9 K$ R% U) i
#9 B5 S; f2 o- Y# a8 N
interface GigabitEthernet0/0/18
4 e4 Q/ N1 U: M: P' i; q6 Q#
0 p* L: V5 T+ m0 B; tinterface GigabitEthernet0/0/19
2 v2 [1 n8 r7 D& y/ |4 j8 }8 O4 ~1 ?1 D#
9 b4 n8 C! l/ ]* E/ `interface GigabitEthernet0/0/20
7 H {: f/ e9 z! \( |#
% Q4 R- F0 O$ D$ Kinterface GigabitEthernet0/0/21
( N" q& m0 w: p# m0 X8 \0 ~- `/ I L# R
interface GigabitEthernet0/0/22& a4 ^0 T& z( h7 A5 x
#
6 o2 ^" J3 P, e2 V& o& I$ Dinterface GigabitEthernet0/0/23
+ j, d& K/ R7 h' \; T#
" P. I- h$ u( W7 g. binterface GigabitEthernet0/0/24$ r# o2 j( X/ B3 e$ u
#
: P& ], W8 D) _ x* k" Einterface GigabitEthernet0/0/25
3 W$ R- q% W5 j! s#7 l% q7 A; w: T' o9 p( N$ {3 X
interface GigabitEthernet0/0/261 o. V' b. C! g3 e+ C# B
#/ N6 ~! k m) ^+ m! J7 K# L
interface GigabitEthernet0/0/279 j2 Z8 X0 ?5 v& j
port link-type trunk1 w, `/ L0 e0 i; {0 U( Z
port trunk allow-pass vlan 2 to 4094+ v& x9 I9 k0 n7 T5 ?
#% {& A$ m2 B; }8 h4 U/ u$ T0 G H/ A$ {
interface GigabitEthernet0/0/28( Y6 {- _+ Z6 M! d7 j
port link-type trunk3 Q& z1 y' w4 W9 m9 z& J# s9 W8 ^
port trunk allow-pass vlan 2 to 40942 {+ x+ A" X+ f; U) z
#
, _! x4 V( {/ S. O0 b) {interface NULL0
3 W- U h- k' ~0 @6 V#' F7 ~. p4 K" m; r8 { _. _
ip route-static 0.0.0.0 0.0.0.0 10.17.10.19 r* j; [& _; a7 |
#9 z: e( H) E# ]' }7 K
user-interface con 0! ` o2 ~* Y2 m0 o; |! W* w
authentication-mode password/ Z* v, Q. i! `: s: s$ D3 X
set authentication password cipher $1a$eS#yO#@1$'$Zh^9;z70=UpQ|I,URtw,V@1iR3/v@Imk6*/@#[PS$6 ~' ^1 M! H1 ?
user-interface vty 0 4
5 L% c9 K: `( F authentication-mode aaa
6 f1 Q9 x1 m* K; J ~ user privilege level 15
4 v/ s7 U7 \% p protocol inbound telnet
5 O0 g/ d; O( W Tuser-interface vty 16 20
2 Z$ W+ e+ g( a2 [. b, h0 l8 \3 T1 y [#
0 Y4 K; H6 L" A- \& Treturn, e0 v# V2 _. Y7 |- D! R
" f) X' {4 f) U% J% t: a* R
, _ ]4 o% ?* w0 ] |
|